Secure IT infrastructure is a foundational element for organizations in the digital landscape. It not only protects sensitive information but also ensures operational continuity. Key components, such as encryption and access controls, are essential in mitigating security risks. However, the effectiveness of these measures often hinges on a well-structured strategy. Understanding how these elements work together can reveal critical insights into enhancing online security. What are the implications of neglecting such infrastructure?
Understanding Secure IT Infrastructure and Its Importance
A secure IT infrastructure serves as the backbone of organizational operations, safeguarding sensitive data and ensuring system integrity.
By addressing network vulnerabilities through proactive measures, organizations can mitigate risks that threaten their operational continuity.
Data encryption further fortifies this infrastructure, protecting information from unauthorized access.
Ultimately, a robust security framework empowers organizations to maintain their autonomy while fostering trust among stakeholders.
Key Components of a Robust IT Security Strategy
Establishing a secure IT infrastructure necessitates a comprehensive security strategy that encompasses various components designed to protect organizational assets.
Key components include well-defined security policies that establish protocols for data management and access control, alongside rigorous threat assessments that identify vulnerabilities and potential risks.
Together, these elements form a resilient defense framework, empowering organizations to maintain operational integrity while safeguarding sensitive information.
Best Practices for Protecting Your Online Assets
Protecting online assets requires a systematic approach that integrates multiple best practices to mitigate risks effectively.
Implementing robust data encryption ensures that sensitive information remains secure during transmission and storage.
Additionally, establishing stringent access controls restricts unauthorized users, safeguarding critical data from breaches.
Together, these measures create a fortified environment, enabling organizations to maintain their digital integrity and uphold their commitment to freedom and security.
Tools and Technologies to Enhance IT Security
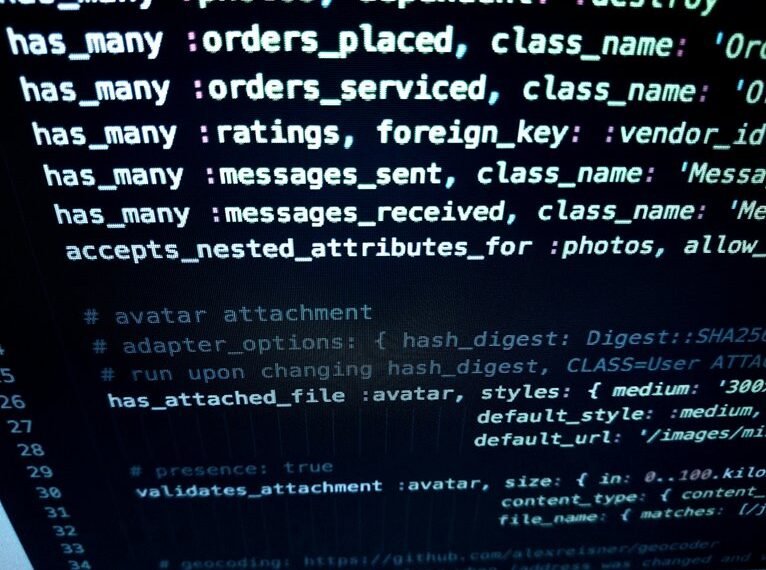
While organizations strive to enhance their IT security posture, leveraging the right tools and technologies is crucial for effective risk management.
Implementing advanced encryption protocols ensures data confidentiality, while conducting regular security audits identifies vulnerabilities and compliance gaps.
Together, these strategies empower organizations to create a resilient IT environment, safeguarding sensitive information and maintaining operational integrity in an increasingly complex digital landscape.
Conclusion
In an increasingly digital landscape, the integrity of an organization’s online operations hinges on a secure IT infrastructure. By implementing comprehensive security strategies and employing advanced tools, businesses can significantly reduce vulnerabilities. However, as cyber threats evolve, can any organization afford to overlook the importance of continuous improvement in their security measures? Ultimately, the resilience of an organization not only protects its assets but also fosters trust among stakeholders, ensuring compliance and operational continuity in a competitive environment.