The significance of a secure IT infrastructure cannot be overstated in today’s digital environment. Organizations must implement essential security measures such as firewalls, encryption, and access controls to protect sensitive data. Regular assessments and updates are crucial to counteract increasingly sophisticated cyber threats. However, the challenge lies in maintaining a proactive stance. What are the key components of an effective security strategy, and how can organizations ensure they are adequately prepared?
Key Components of IT Security You Need to Know
While organizations increasingly rely on digital networks, understanding the key components of IT security becomes imperative for safeguarding sensitive information.
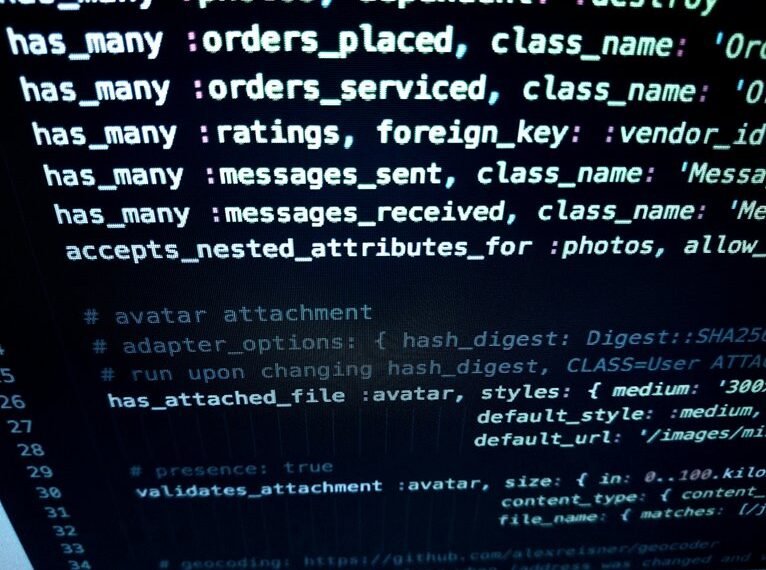
Effective firewall configurations serve as a critical barrier against unauthorized access, while robust encryption protocols ensure data integrity and confidentiality during transmission.
Together, these elements form a foundational strategy that protects organizational assets, enabling stakeholders to operate with greater freedom in a technologically driven landscape.
How to Assess Your Current IT Infrastructure Security?
Assessing the security of an organization’s IT infrastructure requires a systematic approach that evaluates existing measures against current threats.
Conducting a thorough vulnerability assessment identifies weaknesses within systems, while regular security audits ensure compliance with best practices.
This dual strategy empowers organizations to adapt proactively to evolving risks, thereby enhancing their overall security posture and safeguarding critical assets against potential breaches and exploitation.
Practical Strategies for Implementing Security Measures
How can organizations effectively implement security measures to safeguard their IT infrastructure?
By adopting a comprehensive risk management framework, organizations can identify vulnerabilities and prioritize their mitigation.
Effective access control mechanisms should be established to ensure only authorized personnel can access sensitive data.
Regular audits and updates of security protocols further enhance defenses, fostering a proactive approach to maintaining a secure IT environment.
The Importance of Continuous Education in IT Security
Implementing robust security measures provides a foundational layer for protecting IT infrastructure, yet the landscape of cybersecurity is constantly evolving.
Ongoing training and skills development are critical for IT professionals to stay ahead of emerging threats. Continuous education fosters adaptability, ensuring that teams possess the latest knowledge and techniques required to mitigate risks effectively, thereby maintaining the integrity and security of organizational assets.
Conclusion
In the realm of IT security, the adage “an ounce of prevention is worth a pound of cure” holds profound significance. Organizations must recognize that a proactive approach to securing their IT infrastructure through robust measures—such as firewalls, encryption, and access controls—is essential to safeguarding sensitive data. Regular audits and ongoing education are not merely best practices; they are critical components in adapting to the ever-evolving threat landscape, ensuring both compliance and resilience against potential breaches.