A secure IT infrastructure is critical for safeguarding sensitive information within organizations. Key components include network segmentation, access controls, and multi-layered security frameworks. These elements work together to mitigate the risks posed by evolving cyber threats. However, merely implementing these strategies is not sufficient. Organizations must also consider ongoing updates and incident response protocols. Exploring the nuances of these practices reveals deeper insights into creating a resilient digital environment.
Key Components of a Secure IT Infrastructure
While many organizations recognize the importance of cybersecurity, the foundational elements of a secure IT infrastructure are often overlooked.
Key components include network segmentation, which isolates critical assets to minimize exposure, and access control, ensuring that only authorized personnel can access sensitive data.
These strategies create layers of security that enhance resilience against cyber threats, ultimately safeguarding organizational freedom and integrity.
Best Practices for Protecting Your Online Systems
Building upon the foundational elements of a secure IT infrastructure, organizations must implement best practices to protect their online systems.
Effective password management is crucial, ensuring robust authentication methods and regular updates to prevent unauthorized access.
Additionally, network segmentation minimizes exposure to vulnerabilities by isolating sensitive data and systems, thereby enhancing overall security posture and enabling more effective incident response strategies.
Tools and Technologies for Enhanced IT Security
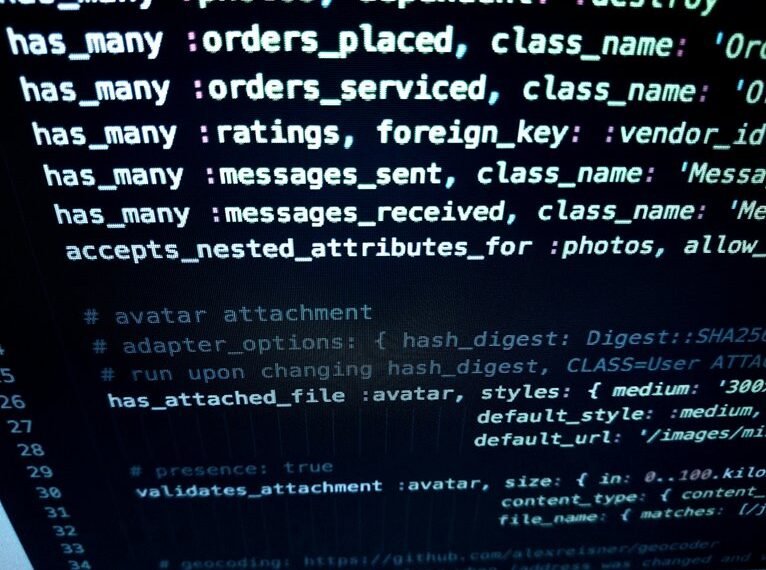
As organizations confront an increasingly complex threat landscape, the integration of advanced tools and technologies becomes essential for enhancing IT security.
Sophisticated encryption methods safeguard sensitive data, while robust threat detection systems identify vulnerabilities and potential breaches in real-time.
Utilizing these technologies not only fortifies defenses but also empowers organizations to maintain operational integrity and independence in a dynamic digital environment.
How to Respond to Security Breaches Effectively?
Responding to security breaches requires a systematic and well-coordinated approach to mitigate damage and restore normal operations.
Effective incident response involves immediate containment, thorough investigation, and recovery efforts. Additionally, clear breach communication is crucial to maintain stakeholder trust and transparency.
Organizations must develop and regularly update their response plans, ensuring readiness to address potential vulnerabilities and uphold their commitment to security.
Conclusion
In an era where cyber threats loom ever larger, the integrity of a secure IT infrastructure hangs in the balance. Organizations must remain vigilant, continuously adapting their strategies to counter emerging vulnerabilities. The implementation of best practices and advanced technologies is crucial, yet the question remains: are they truly prepared for the inevitable breach? As the digital landscape evolves, only those who proactively fortify their defenses will withstand the onslaught, safeguarding their sensitive data from the shadows that threaten to engulf them.